Network Management for IP and Storage
Storage systems, whether or not coupled with editing systems, MAMs or other production-related data systems within broad- cast facilities, are all headed in the direction of IP-based infrastructures.
Regardless of whether users are leveraging fibre channel or Gigabit storage, cloud technologies or simply augmenting their conventional on-premises systems in the central equipment room—the technologies now dominating the next-generation approaches to facility integration are becoming IP-based in every aspect.
Technologies for the use of IP in real-time media networks are rapidly moving into the production and routing infrastructure domains as we steadily progress towards implementation of the developing standards, including SMPTE ST 2110 and ST 2022-6.
WHAT’S LACKING?
What may generally be lacking in the “grand plan” for broadcast facilities is an ideal, consistent and interoperable network management system that can provide not only the control structures for studio video over IP (SVIP), but could become the logical extension to services like storage management, business process/workflow, direct uplink into the cloud and many other potentials.
There is still a lot to be accomplished in this area. Through the outstanding efforts and continuous work by industry forums and associations, including the Advanced Media Workflow Association (AMWA) and the Video Services Forum (VSF); alongside the Alliance for IP Media Solutions (AIMS) and in conjunction with the Joint Task Force on Networked Media (JT-NM), the industry is helping to shape the requirements and recommendations that can make the difference in flexible, reliable interoperability on a network-centric IP architecture.
Tasks essential to interoperability and sustainability (i.e., the ongoing management of systems at a software-defined level) are generally grouped under the heading of “network management.” IT professionals understand the basics of the processes and unfortunately often approach their needs and objectives through the grueling process of trial and error.
For many well-designed network centers, strict adherence to network management is what keeps the systems functioning. In systems where administrators have not been fortunate to have an overarching plan due to budgets, staff changes, inexperience or such, network management can be perplexing and is likely approached on an “as needed” adventure through the day-to-day operations of the entity.
The professional video industry's #1 source for news, trends and product and tech information. Sign up below.
In the upcoming paradigm shift into SVIP on Professional Media Networks (PMN), the trial-and-error approach will not work. As a primer to what network management involves, we’ll now look at the fundamentals of network management, sometimes referred to as network management systems (NMS), in IT vernacular.
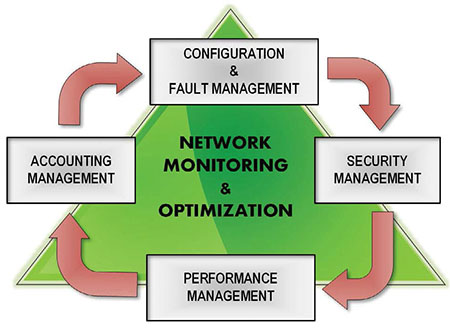
Fig. 1: Processes and procedures typically employed in a network monitoring system (NMS), which are applicable in real-time studio video over IP applications and for storage management systems.
Network management consists of these factors and derivatives: configuration, fault, security, and performance, and accounting management (Fig. 1). The depth and practices involved in these network management tasks can be applied in differing ways depending upon the size or scale of the network involved, and the types of traffic that flow on the network.
CONFIGURATION AND FAULT MANAGEMENT
Knowing the impacts of varying versions (including updates) to software and hardware is a key objective in configuration and fault tolerant management. The processes involve monitoring the network and system configuration information so that the effects on operations within the network can be tracked and managed accordingly and consistently.
Important to these objectives is configuration file management—the verification that new config-files do not degrade the integrity of the network before an actual implementation takes place. Inventory and software management includes the discovery of all the network devices (a dynamic process that lists devices found on the network) and in some cases, an analysis of the software versions present (and past) so that regression testing, if necessary, can be administered without undo impacts on the network or its associated/connected peripherals.
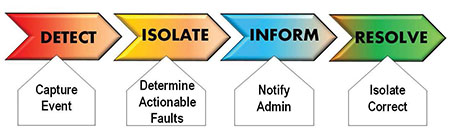
Fig. 2: Steps in fault management and resolution. In Professional Media Networks (PMN), these steps may be provided on an audit network, which is specifically configured as a “watchdog” and “reporting” system that is designed to detect anomalies that humans and visual perceptions might not see or find.
In the PMN, fault detection (see Fig. 2 for fault management steps) may be captured directly by devices and reported to the controlling system. Trend analysis and awareness, along with integral audit networks (described later), can aid in the processes of fault detection, prevention or correction, especially in media-centric IP-video networks.
PERFORMANCE MANAGEMENT
Two areas that impact performance management are: (a) the monitoring, measuring and assessing, plus the reporting of those metrics established pursuant to the network design and functionality; and (b) the service level agreement in place when third-party providers are involved.
Storage management may use applications such as a MAM as the “orchestrator.” The process looks at how well activities such as file-transfers between storage tiers are working; migration to archive; backup systems; or delivery of files to the workstations.
The tasks are continually monitored in the background and are quite useful to the system administrator. As workflows and work processes change (an often-regular activity in content creation and delivery applications), the level of activities required by certain sections of the MAM and storage systems may be improved by adjusting parameters, workflow steps or the time of the tasks, accordingly. This is where performance management is valuable and functionality is often available in enterprise-level MAMs and storage platforms.
When services rely on third-party resources, such as network connections (WANs or MANs or when a service provider is engaged for other services, a written agreement between the provider and the customer—an SLA)—will contractually bind the expected performance level of network services. SLAs consist of agreed-upon metrics that should be realistic and measurable for each side of the contracted parties.
At a device level, SLA performance metrics may include CPU utilization, big buffer/medium buffer allocation, misses or hit ratios and memory allocation. Device-level performance statistics are critical to gauging and optimizing the performance of protocols that drive applications and computation power at higher levels.
For network routers, switches, aggregation devices and other components that support these various higher-layer protocols, performance statistics and technologies for intercity and intrafacility functionality should be monitored, collected and reported to gauge the effectiveness and efficiency of the network and then referenced to the SLA contract.
TUNING AND ANALYSIS
Compared to conventional IT or back-office data traffic, the flows on PMNs will increase significantly and be quite “dense”—that is, signals will be continuously running at or near the interface data link rate (e.g., 10 Gbps or 25 Gbps). Backbones connecting the aggregation points will run at rates in 40 Gbps and 100 Gbps profiles. Such activities will place a high demand on network resources.
For routine workflows and applications, the rates are unlikely to waver—that is, they will be consistent with the uncompressed video data rates for the applicable resolutions (i.e., multiples of 3 Gbps per 1920x1080p stream or dual-stream UHDTV/4K at 12 Gbps per path). PMNs, as a natural course, will be tuned (i.e., configured) for specific protocols and for prescribed data rates, buffer levels and essence flows. They will not be expecting variations in the streams unless specifically requested (re-subscribed) by the control systems.
Historically, network managers typically had only a limited view of the types of traffic running on their networks. In PMNs, where real-time services cannot be burdened by outside non-media-related influences—the network traffic will be confined to specific forms and structures.
Back-office traffic (email, office applications or social media) must be strictly forbidden on PMNs; in similar fashion to enterprise-class storage systems (using fibre channel or Gigabit Ethernet) where dedicated devices are optimized only for the storage data traffic specific to media files. Control and metadata for storage solutions are carried on a separate network, through separate switches and never cross into the storage data traffic itself.
Traffic profiling technologies provide detailed views of the flows in the network. In the IT world, two familiar technologies (RMON probes and NetFlow) enable the collection of these traffic profiles. In the PMN, this process will likely be vendor-specific and tailored to the exact forms of essence (video, audio and ancillary data) that the network will carry.
Accordingly, “big data” analysis techniques may well find their way into the next-generation PMN, providing new analysis insight into the real-time topologies.
SECURITY MANAGEMENT
Controlling access to network resources, according to provisioning guidelines established by the users or administrators, is the target goal in security management. Security involves regulation and monitoring of authorizations and authentications, and provides accounting (collecting and reporting) for billing, auditing or other designated purposes.
The PMN, like conventional data networks, cannot be subjected to the risks of intentional or unintentional sabotage. Processes in the security management subsystem monitor the normal routine operations (e.g., users logging onto a network resource, refusing access to those who enter inappropriate access codes).
PMNs will have to deal with influences such as USB files being added to a graphic system that then permeate through the PMN with unintended consequences, as well as unauthorized changes to the network topologies (e.g., the addition of an IP-camera, which isn’t automatically registered into the system).
Audit networks, intended to record and track activities, changes and even collect unrecognizable anomalies (e.g., minor network glitches, dropped packets, temporary and short-term oversubscriptions or excessive latency) may become a mainstream part of the PMN going forward.
Numerous other concerns and issues will become obvious as IP crosses the boundaries from file-based workflows into real-time dedicated (PMN) solutions. Users will soon need to develop sets of “best practices” and model configurations (topics beyond the level of this article at this time).
Needless to say, for PMN applications, users should leverage available manufacturer resources and/or consult with experts (e.g., systems integrators) who are experienced and familiar with all the aspects of security, control and IP implementation.
Karl Paulsen is CTO at Diversified (www.diversifiedus.com) and a SMPTE Fellow. Read more about this and other storage topics in his book “Moving Media Storage Technologies.” Contact Karl atkpaulsen@diversifiedus.com.

Karl Paulsen recently retired as a CTO and has regularly contributed to TV Tech on topics related to media, networking, workflow, cloud and systemization for the media and entertainment industry. He is a SMPTE Fellow with more than 50 years of engineering and managerial experience in commercial TV and radio broadcasting. For over 25 years he has written on featured topics in TV Tech magazine—penning the magazine’s “Storage and Media Technologies” and “Cloudspotter’s Journal” columns.
