EAS System Target of Undead Prank
The professional video industry's #1 source for news, trends and product and tech information. Sign up below.
You are now subscribed
Your newsletter sign-up was successful
ALEXANDRIA, VA.—On Feb. 11 at 2:33 p.m. local time, TV station KRTV in Great Falls, Mont., saw zombies take over the broadcast in the middle of the “Steve Wilkos Show.” As two young people bickered onscreen, emergency tones burst onto the program’s audio, a crawl began at the top of the screen and an ominous, distorted voice described an apocalypse where the dead were rising from their graves and walking the earth.
In the wake of the Sept. 11, 2001 terrorist attacks, broadcasters were required to update their Emergency Alert System to enable more reliable public information in the event of serious events such as weather disasters. Stations across the country installed new approved products, and for most of these stations the system has worked perfectly. A handful, including KRTV in Montana and WBUP in Marquette, Mich., had the zombie alert go to air.
The FCC declined to comment for this article and referred TV Technology to the Federal Emergency Management Administration. A spokesman for FEMA, Dan Watson, released this statement about the event:
“This appears to be a breach of security of a product used by some local broadcasters. FEMA’s integrated public alert and warning system was not breached or compromised, and this had no impact on FEMA’s ability to activate the Emergency Alert System to notify the American public. FEMA will continue to support the FCC and other federal agencies looking into the matter.”
PASSWORD MANAGEMENT
Although government agencies have not yet released reports on the exact chain of events that led to the spoofed announcement, industry insiders are pretty sure it was caused by lax password management and ineffective Internet firewalls.
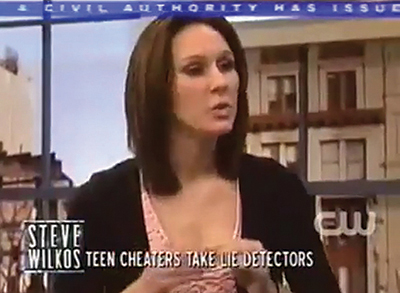
Great Falls Mont. station KRTV’s broadcast of the “Steve Wilkos Show” was interrupted with a hoax “zombie alert.” “The recent unauthorized access of a small number of emergency alert units in the field was apparently made possible by equipment left exposed to the open public Internet, with no firewall protections or other measures, and without factory default passwords having been changed,” said Edward Czarnecki, senior director for strategy, development and regulatory affairs for Monroe Electronics, a Lyndonville, N.Y.-based manufacturer of EAS products.
“We are not intending to be critical of our broadcast partners—far from it,” Czarnecki said. “We are deeply sympathetic that broadcast engineers have been thrust into some serious IT engineering challenges to accommodate CAP EAS, with little in the way of operational best practices provided for them along the way.”
The professional video industry's #1 source for news, trends and product and tech information. Sign up below.
Broadcasters have had a lot to contend with in the past decade, including the digital buildout, spectrum repacking and often-bewildering shifts in regulations and technology. Legislation such as the CALM Act made life anything but calm for broadcasters, and stations in smaller markets had to do everything that all other stations were required to do—and they had to do it with smaller staffs and fewer resources. That made them potentially vulnerable to increasingly sophisticated Internet attacks.
On Feb. 12, a day after the zombie hoax, Cynthia Thompson, station manager for WBUP-TV in Marquette, Mich., announced in the station’s blog that the perpetrator had been caught. Her blog posting gave no additional information about the identity or location of the prankster.
Also on Feb. 12, the FCC issued an “urgent advisory” regarding security for EAS equipment at broadcast facilities:
“All EAS participants are required to take immediate action to secure their CAP EAS equipment, including resetting passwords, and ensuring CAP EAS equipment is secured behind properly configured firewalls and other defensive measures. All CAP EAS equipment manufacturer models are included in this advisory.”
VERY SERIOUS
The broadcasting industry responded to this security breach very seriously. A chief engineer at a network O&O station said privately that he thought the prank was amusing, but network management almost immediately instructed him and his fellow engineers to ensure that all steps were taken at their stations to eliminate the chance of something similar happening.
As for what the actual on-air alert looked and sounded like, it can easily be found by searching on YouTube for “emergency zombie broadcast.” The hoax audio, which sounds like a man’s voice that has been passed through a device to disguise its sound, was not created for this prank attack; on the same YouTube results page as the KRTV-TV broadcast of the bogus alert, there is a video uploaded on Sept. 27, 2009, with exactly the same audio. The EAS zombie prankster obviously stole this earlier audio, which the original uploader stated was for a Halloween party prop.
After the attack, two popular manufacturers of EAS products for broadcasters, Monroe Electronics and Gorman-Redlich, put information on their home pages to advise broadcasters about securing their equipment. Still, when a story based in a highly technical industry such as broadcasting gets out to the general public through the mass media, there’s bound to be confusion.
“There has been a lot of rumor and misinformation circulating about this event, including from security ‘experts’ with very little experience in either broadcasting or EAS,” Czarnecki of Monroe Electronics said. “This is unfortunate—even dangerous—as this kind of hype is a distraction from the key issues at this moment, which are to secure your equipment and to secure your station.”
Czarnecki said that one recurring bit of misinformation is that this was a “backdoor” attack.
“There is no evidence that suggests any access to these devices by means other than a front door entry,” he said. “The intruder logged straight into a device left open on the Internet, using an unchanged default password. As such, I’m not sure this it should actually be called a ‘hacking event’ at all—it was certainly a case of unauthorized access, and that in and of itself is a fairly serious offense.”
FEMA’S ZOMBIES
One irony to come out of this is that FEMA itself has used the concept of a humorous “zombie attack” to encourage Americans to be ready for actual disasters. In a video by the news blog Newsy dated Sept. 8, 2012, FEMA was shown using “zombie preparedness” to get people to think about what they would need to be ready in an actual emergency. Apparently, this method to encourage citizen awareness remains undead even today.
Engineers at TV stations have always been knowledgeable about broadcasting equipment. At many stations today, they are also expected to be the IT experts as well. The general public may think that one type of electronic technology is pretty much like any other, and they probably also think that TV stations are all flush with cash and staffed to the gills with highly trained employees. Perhaps this is because most stations broadcast error-free programming for days on end, giving viewers the impression that the process is effortless.
Most broadcasters and federal officials breathed a sigh of relief that this EAS hoax message turned out to be innocuous, considering how much mischief someone could have caused. The good news is that it will never be as easy again.
Bob Kovacs is the former Technology Editor for TV Tech and editor of Government Video. He is a long-time video engineer and writer, who now works as a video producer for a government agency. In 2020, Kovacs won several awards as the editor and co-producer of the short film "Rendezvous."